WHAT IS
STABLE AGILITY?
To achieve stable agility, organizations must strike a balance between achieving foundational best practices, operational efficiency and continuity for employees and being flexible in adopting new technology and processes to adapt to the ever-changing landscape of the workforce and business environment.
RIVAL
PRODUCT SUITE
RIVAL RECRUIT
Rival Recruit empowers organizations to source, recruit and hire the best talent, add precision to their strategy and maximize their technology investment. It is pre-populated with over 700M passive candidate profiles, AI-enabled recommendations for prioritization and communication, interview scheduling and conversational messaging, branded career sites, recruitment marketing and analytics.
RIVAL ENGAGE
Rival Engage empowers organizations to source, recruit and hire the best talent, add precision to their strategy and maximize their technology investment. It is pre-populated with over 700M passive candidate profiles, AI-enabled recommendations for prioritization and communication, interview scheduling and conversational messaging, branded career sites, recruitment marketing and analytics.
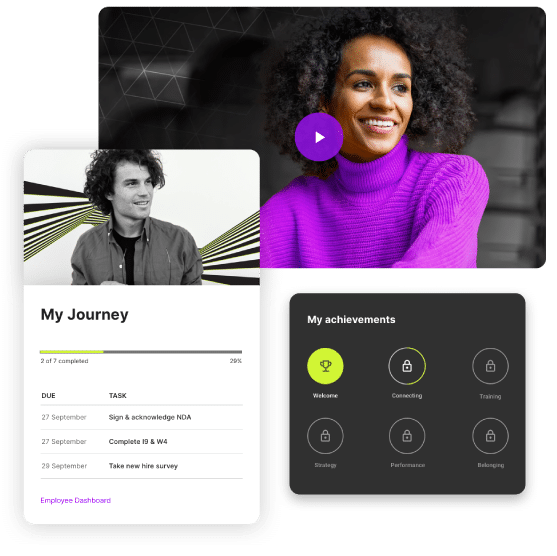
RIVAL ONBOARD
Rival Onboard is the engine powering tailored experiences from source to hire to retire with agility and scale. Onboard streamlines and integrates data, workflows and systems into a unified experience to empower people to work better. It includes journeys, engagement, integrations and compliance for the key elements of the employee lifecycle, including new hire onboarding, crossboarding and offboarding.
Rival Learn
Transform the employee experience by aligning learning to organizational strategy and individual development needs. The solution provides flexibility to enable you to deliver personalized curriculum on any device to drive engagement and retention. Rival Learn is a robust solution that drives compliance across your workforce at scale.
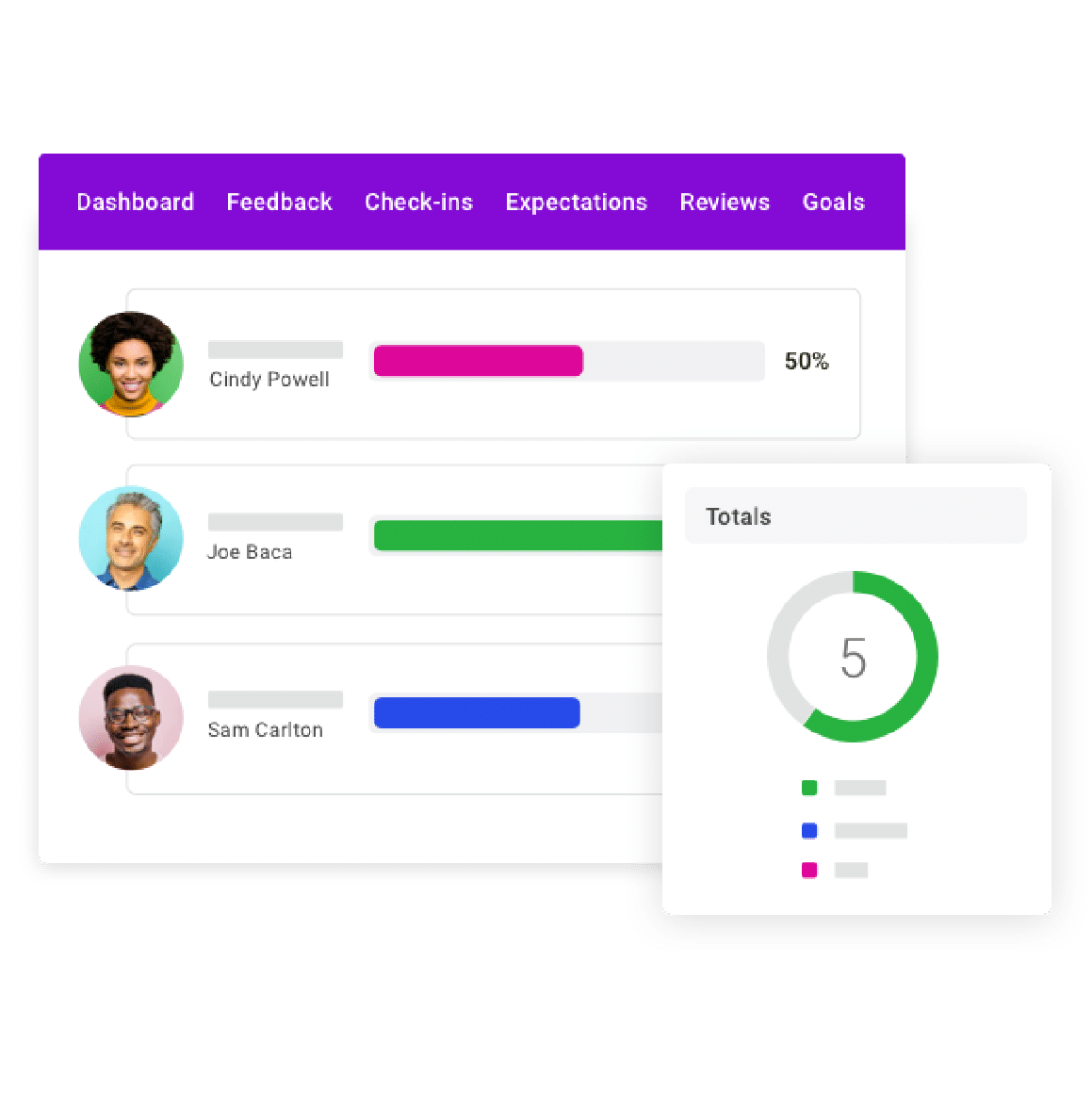
RIVAL PERFORM
Rival Perform accommodates multiple strategies across the performance management spectrum. Go beyond traditional approaches to employee performance management with a more agile, flexible solution. Deliver real-time, actionable feedback that employees crave. Empower your managers, identify and prepare talent for their next role and deliver a more engaging, continuous performance experience across the employee lifecycle.